Cyber attacks paralyze major sites
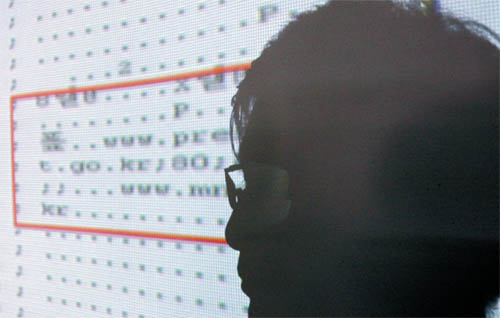
Chang Seok-hwa, team leader of the Cyber Terror Response Center under the National Police Agency, explains yesterday about a program that launches denial of service attacks on several major Web sites. [YONHAP]
The National Intelligence Service suspects North Korea or its sympathizers may have been behind the attack, according to sources who spoke on condition of anonymity. The spy agency briefed some lawmakers on an individual basis or showed written reports that mention North Korea as the suspected attack source. The spy agency will report to the National Assembly intelligence committee today with its analysis, the sources said.
In the United States, 14 U.S. government sites, including those of the White House and the New York Stock Exchange, were also knocked out by hackers over the same hours. The suspected link between the two countries hasn’t yet been confirmed.
The Korea Information Security Agency said yesterday a coordinated cyber attack was launched on the Blue House, National Assembly, Foreign Ministry, Defense Ministry, the ruling Grand National Party, Nonghyup bank, Shinhan Bank, Korea Exchange Bank, the online shopping mall Auction, top Web portal Naver and the Chosun Ilbo newspaper. From as early as 6 p.m. Tuesday, access to those sites was either impossible or unusually slow.
The 14 Web sites attacked in the U.S. include the Treasury Department, Secret Service, Federal Trade Commission and the Transportation Department. The initial U.S. attack was made on July 4.
Although so-called “denial-of-service” attacks have been launched against the Blue House and other government agencies before, this is the first time that simultaneous attacks on almost a dozen high-profile Web sites have happened in Korea. Those sites attacked haven’t reported any compromise of data.
Mail and blog services by Korea’s top portal Naver, operated by NHN, were down from around 6:20 p.m. on Tuesday. Although their blog service recovered by midday yesterday, its mail service had yet to bounce back fully as of late yesterday afternoon. “With the particular nature of denial-of-service, all we can really do is block out service so that our servers will not go down, which we have been doing since Tuesday,” said Kwak Dae-hyun, an NHN spokesman.
According to the Korea Information Security Agency, hackers used distributed denial-of-service, or DDoS, flooding Web sites with requests from a collection of compromised computers and making them inaccessible to the general public. Those compromised computers are referred to “zombie computers,” which the hackers create by remotely hijacking vulnerable computers via e-mail or malicious code without the computer owners’ knowledge. The information agency said an estimated 25,000 personal computers were hijacked for the purpose, with some 23,000 of them located in Korea. Prosecutors yesterday found and confiscated one zombie computer from a household in Dongdaemun, central Seoul, to trace the IP address of the hackers.
The police and the National Intelligence Service said those hackers are presumed to be based in a third country, with China and North Korea as possible originating sites. “Past attacks mostly originated from overseas servers but further probes seem necessary to track down the exact location,” said Choi In-seok, an official at the Cyber Terror Response Center under the National Police Agency. “We have yet to find what has motivated the cyberspace attack.”
Roh Seung-kwon, chief prosecutor at the Seoul Central District Court, warned about the possibility that the hackers will launch additional attacks. “Denial-of-service attacks can be made whenever hackers decide,” he said in a briefing. Asked if the assault originated in North Korea, he only said, “That we don’t know yet.” Should the hackers turn out to be Koreans, they will be “severely punished,” he added.
Under the Korean information network law, those who spread malicious code or programs across other computers and cause network malfunctions are subject to up to a maximum five-year prison term or 50 million won ($39,200) fine.
In response to cyber attacks on major government Web sites, the Joint Chiefs of Staff in Seoul said it was considering raising its defense alert level for information systems. The current level of South Korea’s five-stage Information Operations Condition, or Infocon, is at its lowest, level 5. Raising the level a notch would alert commands of all branches about the increased risk of attack on military networks.
The KISA advises that all Internet users install the latest version of computer anti-virus software and upload a Windows security patch to prevent their computers from serving as zombies. AhnLab Inc., a top local security solutions firm, developed an Internet virus vaccine as an emergency measure to prevent further denial-of-service attacks. It provides it free for any company or individual seeking protection.
“In order to prevent one’s PC from an attack, it’s crucial to install and frequently use anti-virus programs and to update the program as well as the security patch to the latest versions. Also, one must be extremely careful about opening suspicious e-mail, messenger files or URL links,” said Cho Si-haeng, manager of the security center at AhnLab.
By Seo Ji-eun, Cho Jae-eun, Yoo Jee-ho










with the Korea JoongAng Daily
To write comments, please log in to one of the accounts.
Standards Board Policy (0/250자)