Cybercrime sleuths have highly intricate challenges
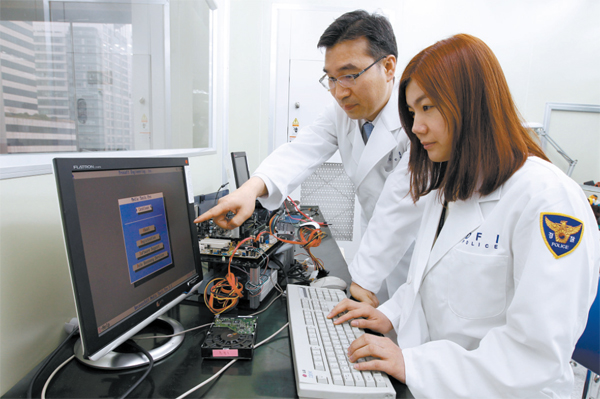
Police officers from the Cyber Terror Response Center of the National Police Agency on Tuesday restore a damaged hard disk to trace cybercrimes that were conducted on a computer. By Kim Seong-ryong
The police then traced the IP addresses and found 10 hackers, including a 39-year-old man surnamed Shin, in three days.
The police said it is very hard to locate these types of hackers, but it was fortunate at the time that they were able to find clues to track them down.
The police said the hackers were preparing another hacking attempt when they were caught.
“We raided the hackers’ secret office and were able to secure digital evidence at the time, but it is very unusual to obtain digital evidence like this,” a spokesman for the NPA told the JoongAng Ilbo. “We also had trouble restoring the data that the hackers deleted when we raided their place.”
In March, a 27-year-old woman surnamed Kim became a victim of phishing, which uses mobile phone messages to lure people into accessing bogus Web sites and dupe them into providing their bank or credit card information.
She reported to local police that she received a text message offering a free fried chicken meal coupon if she installed a game application on her smartphone.
As soon as she downloaded the application, malignant code spread throughout her phone, then about 300,000 won ($268) worth of game items were purchased at an illegal Internet game Web site in her name.
The police requested Kim hand over her smartphone for investigation, but weren’t able to proceed as she refused to hand it over. She didn’t want the police to see her personal information.
“We must check the mobile phone in order to trace how the malignant codes were distributed, but we basically can’t do anything if the victim doesn’t want to let us,” an officer for the NPA said.
The number of cybercrimes have been rapidly increasing recently, and the seriousness of the crimes reached a peak when some hackers, who have not yet been identified, but are suspected to be North Koreans, boldly tried to paralyze or destroy systems of the country’s major banks, including Shinhan and Nonghyup, and broadcasters KBS, MBC and YTN on March 20.
Most of the country’s cybercrime response authorities, including police and the prosecution, as well as Korea Internet Security Agency (KISA), are having trouble managing these problems.
In cybercrimes like the KT case, it is important to secure digital evidence before hackers destroy it.
Under the current law, investigators can request those hacked victims or organizations to hand over digital evidence, but it isn’t mandatory for victims to submit the evidence.
“We usually trace the hacking route from PCs and servers that have been hacked, but most of the victims are reluctant to hand them over to investigators,” Park Sun-tae, director of the hacking response team of the KISA, told the JoongAng Ilbo.
“It makes it impossible to proceed with investigations. And some of the evidence is damaged while investigation agencies recover data.”
This means that the best option for securing important digital evidence for investigators is to get a search and seizure warrant, but there is another problem.
“Digital evidence can be easily destroyed while investigators wait for a court to issue a search and seizure warrant,” Professor Lim Jong-in from the College of Science and Information at Korea University said.
Investigators can raid the suspected crime scene and request a warrant later, but the investigators must be able to provide evidence and finish the raid within 48 hours.
From January, the revised regulations stated that investigators can only copy and print out portions of materials that they consider necessary digital evidence when they raid a suspected cybercrime scene.
“It is almost impossible to finish the investigation within 48 hours because it is hard to obtain such evidence and it takes a long time to analyze digital evidence,” a police officer said.
Experts in the legal circle said the government must revise relevant laws.
“The government must consider establishing laws for cybercrimes that could give more time to investigators when they need to raid a suspected crime scene before a court issues a search and seizure warrant,” Koo Tae-un, head of Tek & Law, a law firm, told the JoongAng Ilbo.
In advanced countries such as the United States and United Kingdom, they manage cybercrimes aggressively as they consider them a serious threat that could damage the country’s important systems and public safety.
The U.S., for instance, has provided a legal basis so that authorities can swiftly react to cybercrime after 9/11.
The Patriot Act, which treats people attempting cyberattacks as terrorists, is one example.
Under the act, investigators can raid the suspected crime scene and notify their move to a court after conducting necessary action.
“The log-in history of a PC, which is important data in cybercrime investigation, gets deleted within a month,” said attorney Heo Jin-young, who investigated the DDoS attack that occurred in October 26 by-election in 2011. “We must consider adopting the system that the U.S. currently uses.”
By Lee Seung-ho, Kwon Sang-soo [sakwon80@joongang.co.kr]










with the Korea JoongAng Daily
To write comments, please log in to one of the accounts.
Standards Board Policy (0/250자)