Incheon Airport cyberattack traced to Pyongyang

A 39-year-old South Korean game distributor was arrested on Sunday for involvement and charged with violating the National Security Law. The National Intelligence Service helped arrest him, police said.
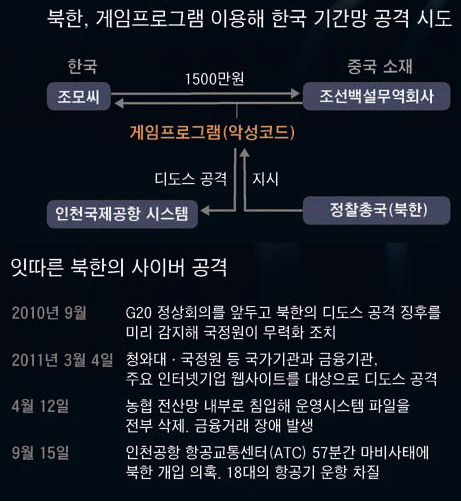
The North Koreans were actually agents from the North’s Reconnaissance General Bureau, and Jo was aware of that, police said.
Jo purchased dozens of computer game software for tens of millions of won, which was a third the cost of the same kind of software in the South. The games were infected with malignant viruses, of which Jo knew, an official at the police agency said.
Jo sold the games to South Korean operators of online games. When people played the games, the viruses used their computers as zombies, through which the cyberattack was launched.
So-called “a distributed denial-of-service attack,” this cyberattack against Incheon International Airport occurred two or three times in March 2011, police said. The attack was fended off by the intelligence authorities in the South.
The police and intelligence authorities also suspect that the North’s Reconnaissance General Bureau is behind a technical glitch in the flight data processor that paralyzed air traffic control at Incheon International Airport for nearly an hour last Sept. 15. It’s not clear if Jo’s viruses were linked. The glitch disrupted the departures of 18 airplanes from the airport. Initially, the Ministry of Land, Transport and Maritime Affairs said it wasn’t linked to North Korea.
The police said they are looking into the possibility that North Korea planted a computer virus as powerful as the Stuxnet virus into the air traffic control at Incheon International Airport.
Stuxnet, allegedly developed by the U.S., is suspected of attacking computer systems at Iran’s nuclear facilities and destroying centrifuges. Around 7,300 computers in South Korea were infected with Stuxnet in January 2011, according to the government.
Some computer experts in the South say that North Korea could try to destroy infrastructure in the South connected with traffic, electricity, power plants and water supplies by hacking into computer systems in the South.
“The North’s Reconnaissance General Bureau has hired hackers with North Korean companies in China and mobilized them for earning foreign currency for the regime or cyber terrors against the South,” said an intelligence official in the South.
North Korea’s Reconnaissance General Bureau, created in February 2009 to lead sabotage campaigns against the South, is known to employ over 1,000 hackers. South Korean and U.S. intelligence agencies also suspect that it masterminded the sinking of the South Korean warship Cheonan in March 2010. The North denies its role in the sinking, which killed 46 South Korean sailors.
Meanwhile, the police said they were also investigating whether Jo provided to the North any personal information of South Korean users of the games he ran, which number over 100,000.
By Lee Chul-jae, Moon Gwang-lip [joe@joongang.co.kr]










with the Korea JoongAng Daily
To write comments, please log in to one of the accounts.
Standards Board Policy (0/250자)