Incidents of spear phishing are on the rise
In the text box, the sender of the email introduced himself as an official from the Ministry of Unification and even jotted down his phone number. Although nothing seemed to be awkward, employees later found out that the attached file sent by who they thought was a trusted source was actually a malicious code when the file was clicked, downloaded and opened.
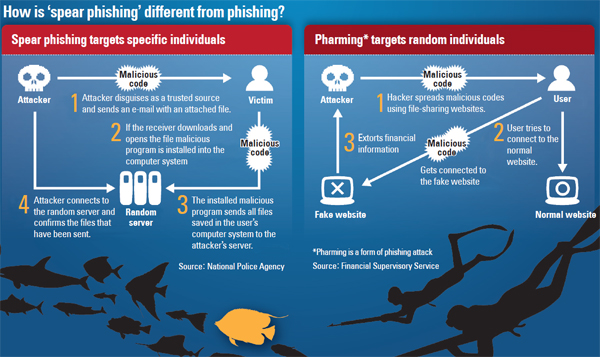
According to information technology security sources last week, damage from so-called spear phishing activities is spreading. Spear phishing is an up-and-coming online scam that targets specific individuals or groups to access classified information by disguising the perpetrator as a trusted source by using a real email ID or company name. It is different from regular phishing activities that target large numbers of random individuals.
Jang Se-yul, head of the National Alliance for Unification, was recently victimized by a spear-phishing scam. Jang is a security expert who studied at Mirim College in Pyongyang, the capital of North Korea, known for fostering hackers in the Communist regime.
According to South Korea’s National Police Agency, Jang received three emails earlier this year on separate occasions from senders disguised as well-known professors and an official from the Ministry of Security and Public Administration. Jang, without suspecting each of the senders, opened one of the files and the malicious code immediately infected his computer. The 1.4 gigabyte files Jang had saved, including documents on North Korean defectors, were then drawn out to an overseas server.
Security industry sources note that spear-phishing scams are usually used in various spy activities that target government organizations, the military and research institutes. Recently, however, they note that scams targeting corporations and individuals seeking financial benefits have become more frequent.
The Financial Supervisory Service earlier this month issued an alert on spear-phishing activities targeting trade settlements. For example, an attacker would hack the email of an exporter or importer by installing a malicious code through spear phishing and take out trade deal information. The attacker would then send an email to a random counterpart and request him or her to send payment to a fake bank account.
“It isn’t easy differentiating the real sender from a fake one because the name of the sender would be written as someone the victim has had long-term partnerships with,” said Jang Hong-je, an FSS official. “We advise businessmen to be on alert, and if the bank account of their trading partners changes then they should double-check by phone or fax.”
Spear-phishing attacks also target individuals and access personal information on mobile devices.
Earlier this month, a group of attackers was caught by police in central Seoul. They were caught for having sent text messages to specific mobile users by writing down their names and asking how they have been with a link below.
“Individuals are more vulnerable to spear-phishing scams because they tend to click on attached files and links even if the sources are unknown,” said Moon Jong-hyun, an official from Inca Internet. “It is very dangerous to save passwords of authentication certificates and photos of individual bank security cards on computers and mobile devices.”
BY SOHN HAE-YONG [angie@joongang.co.kr]










with the Korea JoongAng Daily
To write comments, please log in to one of the accounts.
Standards Board Policy (0/250자)