Hacking ring’s fraudulent ploy hits 108 people
Detailed in the statement were some millions of won worth of transactions settled by a mobile application card that he had no memory of downloading.
What did flash through his mind, however, was a past instance in which he had clicked a link in a text message that prompted recipients to watch a video of the Sewol ferry accident.
The incident on April 16, Korea’s worst maritime disaster that took the lives of more than 300 people, proved to be the bait that lured him into an SMS phishing scam.
“I unconsciously pressed the Internet address,” said the office worker, who refused to give his name, “and I think it was then that a malicious code penetrated my smartphone.”
Seoul police officers have recently put three hackers behind bars for swindling 108 people, including the aforementioned man, and stealing their money and personal data through fraudulent text messages that contained malware.
Once the codes were downloaded onto their victims’ phones, the hackers stole their personal data and financial information, using it to issue an application card and then to purchase mobile gift certificates.
The mobile gift certificates were sold on local online shopping websites at prices 15 percent lower than the initial purchase in cash, and finally converted into yuan for the network’s primary operators in China.
The scam was a part of a joint effort between hackers in China and Korea, authorities here said.
Officers with the Seoul Metropolitan Police Agency’s cybercrime investigation team added that they are currently cooperating with their Chinese counterparts in the search for two more culprits responsible for accumulating 134 million won ($121,000) in total.
In a research paper released earlier this month, Trend Micro, a global security software company headquartered in Tokyo, found that more than 4,000 Koreans have been victimized over the past two years by a group known as the Yanbian Gang, a cybercriminal group operating out of northeastern China.
“In 2014, we took a close look at the Chinese underground market and found that it continued to thrive,” the company wrote in “The South Korean Fake Banking App Scam.”
“But what we did not see was that even cybercriminals in remote parts of the country - Yanbian - were successfully profiting from Android mobile banking customers in a neighboring country.”
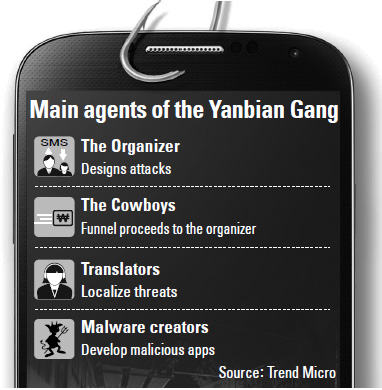
The paper further discussed the key players in the group, who were referred to as the Organizer, the Cowboys, the malware creators and the translators.
Accordingly, the Organizer is the “founding father” of the hacking group, who - while not tech savvy - scouts for new recruits and controls communication among members.
Translators were defined as those who localize threats, in this case the meticulously crafted text messages.
Cowboys, who reside in the same countries as the target victims, collect the proceeds from their financial attacks and send them to the organizer.
“Cowboys use what is called a black card, or fridge cards, to evade law enforcement,” the paper read, adding that the cards, traded via QQ Messenger, “cannot be traced back to the cowboys or anyone they know.”
Malware creators, “the most important members of the gang,” focus on developing mobile malware that evades detection by the authorities and security solutions.
In explaining the operation process, the software company said that fake banking apps are distributed through phishing messages, which in many cases, “come with the ability to uninstall and take the place of the real apps they are spoofing.”
The apps then “continuously and silently” run in the background, leaking confidential information like the user’s name, bank account numbers and passwords.
“A lot of jobless young adults in Yanbian who drop out of school end up landing in the gang,” said Choi Yeong-sam, part of Trend Micro’s local branch. “Some also work for free to learn hacking techniques and go off to organize their own circle.”
Acknowledging the information in the report, the police advised Koreans to download free smartphone applications dedicated to blocking malware attacks.
BY SOHN HAE-YONG, LEE SUNG-EUN [selee@joongang.co.kr]










with the Korea JoongAng Daily
To write comments, please log in to one of the accounts.
Standards Board Policy (0/250자)