[Debriefing] Cryptocurrency hacks
The heist sent a shockwave through the Korean cryptocurrency market, pulling down the price of coins and tokens across the board.
Following the incident, the value of bitcoin, the most well-known cryptocurrency, tumbled by about 7 percent to fall below 8 billion won in Korea for the first time since April.
Here are the basics on how cryptocurrency exchanges can be compromised.
Q. What is cryptocurrency?
Cryptocurrency is a decentralized, peer-to-peer form of electronic currency that uses distributed ledger technology - known as blockchain - to record its transactions.
Cryptocurrency was first introduced in 2008 when a person calling themselves Satoshi Nakamoto developed bitcoin, the most well-known cryptocurrency in the world. The digital currency quickly became popular as proponents argued that the decentralized system is less prone to manipulation because all transaction data is recorded in a public ledger.
Proponents claim that the digital system is more secure than fiat currency because all data is stored in a scattered database, making it virtually unhackable. In order to crack a cryptocurrency, a hacker would need to dig into every single computer on the blockchain, an expensive and implausible feat. A coin is a medium of payment that has its own blockchain where all of its own transactions are stored, while tokens are a representation of a particular asset or utility that is based on an existing blockchain.
In other words, within the cryptocurrency ecosystem, coins are basic money, like a dollar bill. Tokens can play a role similar to coupons and vouchers, or even to stocks and shares, as their value is underpinned by a company.
Q. What is an exchange?
Cryptocurrency exchanges are platforms where virtual currencies like bitcoin and Ethereum are traded. They’re similar to foreign exchange markets, but instead of national currencies, they trade in cryptocurrency.
In some countries, like Japan, exchanges have to receive approval from the government to operate. The Japanese Financial Services Agency has licensed cryptocurrency exchanges since last year.
In Korea, however, cryptocurrency exchanges only have to register as telecommunications companies. The government’s scrutiny of a potential exchange’s capital is lower than in Japan, and investors don’t receive the same protections that they would if they invested with a financial company.
Q. How safe are exchanges?
Currently, there are no government regulations on cryptocurrency buyers other than the requirement that they use bank accounts linked to their real name, which was introduced in January.
The top four exchanges in Korea ? Upbit, Bithumb, Coinone and Korbit ? are required to adopt an information security management system (ISMS) certified by the state-owned Korea Internet & Security Agency (KISA) by the end of the year. This security requirement only applies to information and telecommunication service providers that have annual revenue over 10 billion won or over 1 million daily users. Smaller exchanges that don’t meet these requirements don’t have to use a security management system.
None of Korea’s cryptocurrency exchanges, however, have actually received the certification yet, though they have announced plans to introduce ISMS systems later this year.
The only foolproof cryptocurrency security method is storing it in a cold wallet, which is not connected to the internet. Most cryptocurrency is stored on hot wallets, which are connected to the internet.
The Korea Blockchain Association recommends that cryptocurrency exchange clients save at least 70 percent of their cryptocurrency holdings in a cold wallet.
Q. How do hackers steal information from exchanges?
The most common way of stealing cryptocurrencies is hacking exchanges themselves, which is much easier than trying to manipulate the cryptocurrencies themselves. Some hackers have also used malware to harvest the personal information of cryptocurrency owners.
According to U.S. security company Carbon Black, 27 percent of total hacks this year targeted cryptocurrency exchanges.
In most cases, hackers try to steal information, such as their private keys, and then transfer their cryptocurrencies to their own accounts.
Q. What can a hacker do with stolen cryptocurrency?
It’s unclear exactly what hackers can do with stolen coins. The decentralized ledger means it is difficult for thieves to immediately start trading or spending their ill-gotten funds, but recent cases suggest that hackers can try to launder the stolen coins at decentralized exchanges before cashing out cleaner coins through centralized exchanges, according to Simon Yu, CEO of Storm, a Seattle-based blockchain company.
Decentralized exchanges ensure a higher level of anonymity compared to centralized platforms.
Earlier this year, hackers drained around $500 million worth of XEM tokens from Japanese cryptocurrency exchange Coincheck. NEM Foundation, the issuer of XEM, tagged the stolen tokens as “tainted” in an effort to track their movement. However, despite the tracking effort, most of the stolen funds are thought to have been laundered at exchanges around the world or through dark web channels. This has forced the foundation to call off the hunt.
Q. Isn't the idea of blockchain that cryptocurrency is always traceable?
Cryptocurrency transactions are traceable as they are recorded in ledgers that are open to the public. However, coins are traded from wallet to wallet anonymously, making it difficult to find out the identity of the people behind the trading.
For instance, if hackers turn to dark web channels or wash stolen funds at decentralized exchanges, it becomes virtually impossible to trace the identity of the perpetrators.
Hackers steal millions of coins and trade them anonymously for new coins very quickly, often using automated services on the dark web that mix tainted coins with clean coins.
Although all of these transactions are being recorded in each coin's blockchain, the hackers create such extensive trails that they become virtually impossible to follow.
Even if the trail of interactions could be unraveled, the anonymity essentially ensures that the thief has long disappeared before authorities can reach the end of the trail.
“For such reasons, more exchanges are getting aggressive to comply with KYC [know-your-customer],” explained Yu.
Q. Have there been any major hacks in the past?
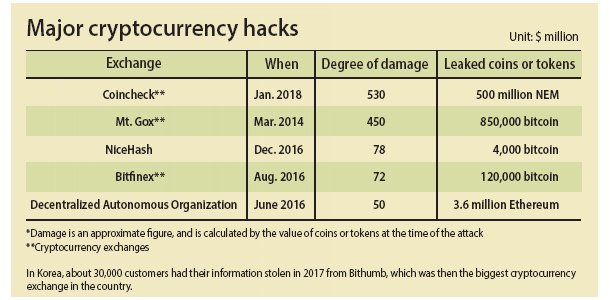
There have been a number of major hacks in the past.
The biggest security breach to date happened in 2004 when about 850,000 bitcoins went missing from Mt. Gox, once the biggest digital coin exchange in the world. The Japanese exchange handled about 70 to 80 percent of all bitcoin transactions in the global market. The total loss was estimated at around $400 million at the time, although today, those coins would be worth more than $5 billion.
The incident forced Mt. Gox to declare bankruptcy and close down its service.
In Korea, Youbit folded in December last year after being hacked for a second time. Youbit is currently operating again after it was sold to CoinBin, another exchange in Korea.
Q. Has stolen cryptocurrency ever been recovered?
There haven’t been any reports of large amounts of stolen cryptocurrency being directly recovered, but losses have been mitigated.
In a public statement released after the recent attack, Coinrail said it was able to “freeze, retrieve and compensate” about 80 percent of the cryptocurrency that was stolen. In this case, the exchange was able to obtain coins or tokens from some of the issuers, equivalent to the quantity that was lost.
For instance, TraDove, the issuer of the BBCoin tokens that were lost during the attack, said in a statement that it has “reached an agreement with Coinrail in which a full recovery of TraDove BBCoin tokens will be credited to these token holders’ accounts.” It is highly likely that, instead of recovering the stolen ones, the companies decided to reimburse the owners with existing “clean” cryptocurrency.
“In most cases, it is not possible, or at least difficult, to recover lost cryptocurrency, because when most companies create tokens, they do not want to have that much power that enables them to track and retrieve tokens at their own discretion,” said Yu of StormX.
Simon explained that exchanges could put a stop to certain wallet addresses and freeze activities if the wallet belongs to centralized exchange.
It is quite unlikely that hackers would put stolen coins or tokens into centralized exchanges first because they know that their activities could be tracked. Yu added that if exchanges store coins or tokens in cold wallets it would be the most effective way to prevent hacking.
BY LEE HO-JEONG, CHOI HYUNG-JO, JIM BULLEY AND JAMES CONSTANT [choi.hyungjo@joongang.co.kr]










with the Korea JoongAng Daily
To write comments, please log in to one of the accounts.
Standards Board Policy (0/250자)