Tapping your smartphone is easy, but protecting yourself is easy too
The answer is yes, especially when it comes to voice calls.
Voice calls on phones nowadays still operate on the same principles used back in the 19th century, when the technology was first developed by the Bell Laboratory in the United States.
The only difference is how the calls are connected. Humans did the work 140 years ago, but now it is done by machines.
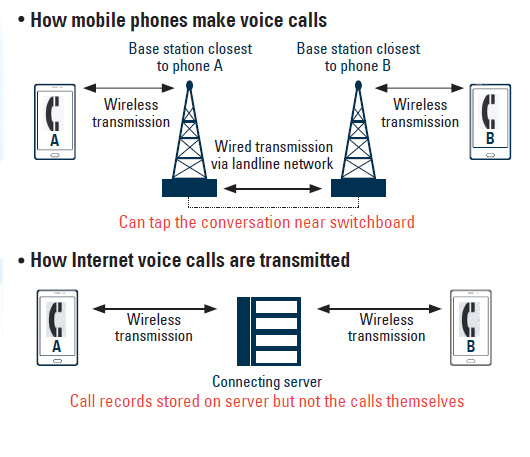
When Mr. A calls Ms. B, only the mobile device and the closest base station are connected wirelessly. Base stations are linked via wires, which can be tapped.
Mobile phone calls are also designed to go through a switchboard before reaching the other party. These switchboards can also be tapped.
Many telecommunication technologies use encryption to boost the level of security, but voice calls on landlines or from mobile phones do not.
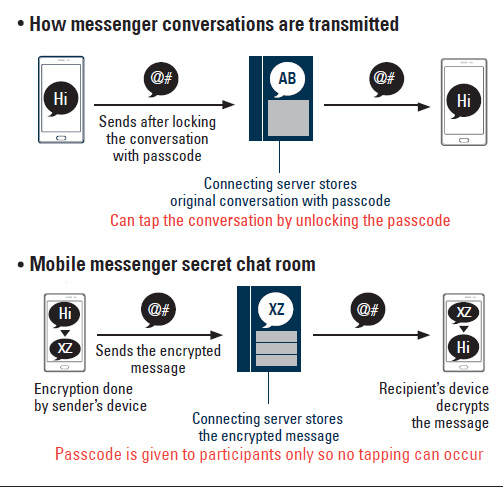
Encryption technologies store raw data after transforming it into a different format. To prevent unauthorized people from accessing the data, the encryption technology uses special passcodes. Decrypting such passcodes is not easy. It takes nearly 80 years for a supercomputer to figure out passcodes generated by 64-byte encryption technology.
But calls via landline or mobile devices can’t use encryption technologies. If each telecom uses its own encryption technology, an SK Telecom customer wouldn’t be able to talk to a friend who uses a different phone company.
Regular text messages are as vulnerable as calls. Penetrating the network from the outside is difficult but technically possible.
Calls over Skype, KakaoTalk’s VoiceTalk and WhatsApp, which use mobile Voice over Internet Protocal (mVoIP), offer encryption mainly because the signals do not have to pass through telecoms’ switchboards.
Korea’s most popular mVoIP service, VoiceTalk, is designed not to store conversations on a server. However, because Internet calls are made over a server, information like who you talked to and how long the conversation lasted are recorded.
Local mobile messengers like KakaoTalk and Line have beefed up their privacy measures by launching a privacy-mode chatroom service, which have been welcomed by users, according to industry analysts.
Regular chatrooms used by mobile messengers transmit and store messages on the operator’s server, which can be hacked. The people who operate the server can also read the conversation.
In the new privacy-mode chatrooms, there is a higher level of encryption. Unless someone actually steals an individual’s smartphone, they cannot read the messages.
Other mobile messengers like NateOn, Line, WhatsApp and Phone & Hush have also implemented that technology. But it cannot be adopted for the messengers’ PC versions.
Many communication apps with advanced security have been introduced in Korea.
Google’s Hangout and Apple’s FaceTime are two apps that enable voice calls and text messages without registering a phone number. Instead of phone numbers, they use e-mail address or Apple IDs, minimizing a user’s identification.
KIPI operates via peer-to-peer communication (P2P) technology, which transmits data from a device directly to another without passing through a server, so the app is free from hacking risks.
Russian messenger service Telegram uses the same P2P communication method. Many people have downloaded it to avoid being spied on.
But the National Intelligence Service snooping scandal is a different story, because it involved special malware that disables security functions in a mobile device.
Such spyware penetrates a smartphone by disguising itself as a mobile application. Then the malicious code disables security functions, snoops on text messages and e-mails and records voice calls, all of which are sent back to the hacker. The spyware even accesses the keyboard to send user passwords and other personal and financial information.
Because it is not easy for normal people to recognize such malware, analysts advise people to be wary of suspicious URL addresses sent via text messages or installing free mobile apps from unverified sources.
“Smartphone users should be really careful when modifying the basic operating system offered by the phone, via methods like ‘jailbreaking,’ which may make the device vulnerable,” said Kim Yong-dae, head of the Korea Advanced Institute of Science and Technology Graduate School of Information Security. “Users should also refrain from downloading apps from unverified app markets, but instead always use official app markets.”
When it comes to operating systems, Apple’s iOS keeps information more secure because the company has not publicly opened its operating system.
Because spyware developers and hackers are less likely to understand how iOS is engineered, it is difficult for them to penetrate it.
Google has opened its Android operating system to expand its mobile platform business quickly and offers the OS to smartphone manufacturers for free. This has made it easy for hackers to download Android’s codes and study how to penetrate them.
BY HAM JONG-SUN [kim.jiyoon@joongang.co.kr]










with the Korea JoongAng Daily
To write comments, please log in to one of the accounts.
Standards Board Policy (0/250자)